Table of Contents
Geofencing: An In-Depth Overview
What is Geofencing?
Geofencing stands as a location-based technology that revolves around the creation of virtual boundaries on a map, usually represented as polygons or circles. These digital confines are generated through GPS coordinates, accommodating a vast spectrum of geographical scales, from small areas like a building or a park to vast regions such as a city or even an entire country. The term “geofence” is derived from combining the words “geographic” and “fence.”
Applications of Geofencing
The primary application of geofencing is to monitor and manage the movements and positions of devices, including smartphones, IoT devices, or vehicles, within pre-established geographical parameters. When a device crosses these boundaries, specific actions or notifications can be promptly activated. Geofencing finds diverse applications, including:
- Location-Based Marketing: Businesses leverage geofencing to dispatch targeted offers or advertisements to users upon their entry into particular geographical zones.
- Asset Tracking: Asset tracking encompasses the meticulous monitoring of valuable assets or vehicles.
- Security and Safety: Geofencing is instrumental in issuing alerts when an individual enters or departs from a restricted area or a region susceptible to disasters.
- Navigation: It facilitates the provision of location-based services, such as furnishing directions or proximity alerts.
- Automation: Geofencing’s capabilities extend to automating various actions, like illuminating lights when one arrives at home.
Components of a Geofence
A geofence has the following components to it:
- Geofence Boundary: The virtual periphery of a geofence materializes by configuring GPS coordinates, and it can manifest in various forms, including a basic circle, a polygon, or a combination of shapes.
- Device Location Data: The geofencing system must be constantly attuned to the location of devices, a task typically executed through GPS or alternative location technologies.
- Actions and Notifications: Predefined actions and notifications spring into action as devices traverse geofence borders. These actions can encompass sending emails, issuing push notifications, or initiating other devices.
Types of Geofencing Algorithms
The choice of algorithm for implementing geofencing depends upon the specific application and the desired trade-offs involving accuracy, efficiency, and complexity. The following are some common algorithms:
- Point-In-Polygon: This algorithm assesses whether a device’s coordinates fall within the designated polygon of a geofence. It proves suitable for uncomplicated geofences, though intricately shaped boundaries may require more complex handling.
- Distance-Based: Calculating the distance between the device and the center of the geofence to determine whether the device is inside the geofence when the distance falls within a defined range. It’s a simple method for creating circular geofences.
- Cellular and Wi-Fi Fingerprinting: This approach estimates a device’s position within or outside a geofence through the utilization of accessible cellular and Wi-Fi signals. It thrives in urban settings but may bear limitations in terms of accuracy.
The implementation of geofencing requires a balance between precision and battery efficiency. More precise algorithms tend to drain more power due to the demand for continuous location tracking. In contrast, less accurate methods can extend the device’s battery life but might generate occasional false positives or negatives.
Geofencing emerged as an important technological tool with various applications encompassing marketing, navigation, security, and automation. The successful implementation of geofencing requires a deep understanding of the chosen geofencing algorithms, the specific use case, and the associated trade-offs between precision and efficiency. It proves to be an invaluable resource for businesses and developers seeking to harness location-based services and notifications.
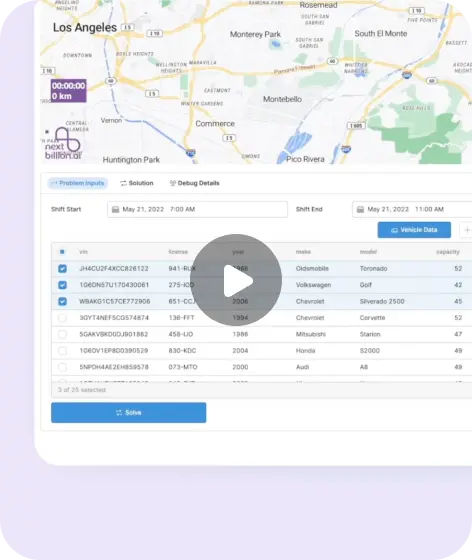
Refer to NextBillion.ai’s Geofence API for more details.
We know that every business is different and we care about your unique needs.
With NextBillion.ai's Map API you get- Large Distance Matrix API with a Matrix size upto than 5000*5000
- Optimal routes with accurate ETAs
- Flexible navigation SDK that's easy to integrate and ready to use for developers
- Quick and accurate location data
- Track and trace routes taken along with other map attributes
- Create custom tiles for your interactive maps. Personalized to fit your brand aesthetic.